— Compliance productivity infrastructure
Compliance
capacity.
No new
headcount.
Springwood is the production system that sits behind onboarding, monitoring, investigations and reporting. Inputs are verified once. Decisions are written as a by-product of the work. The audit file is the working file.
- Built for
- Banks · EMIs · PIs
Funds · Crypto · LE - Scope
- KYC · KYB · KYT
OSINT · SAR · Audit - Deploy
- Platform · API · SDK
White-label · Hybrid
Workspace · 03 sheets
Rev. 2026.05
One customer.
One live picture.
Audit retained
Six modules.
One operational file.
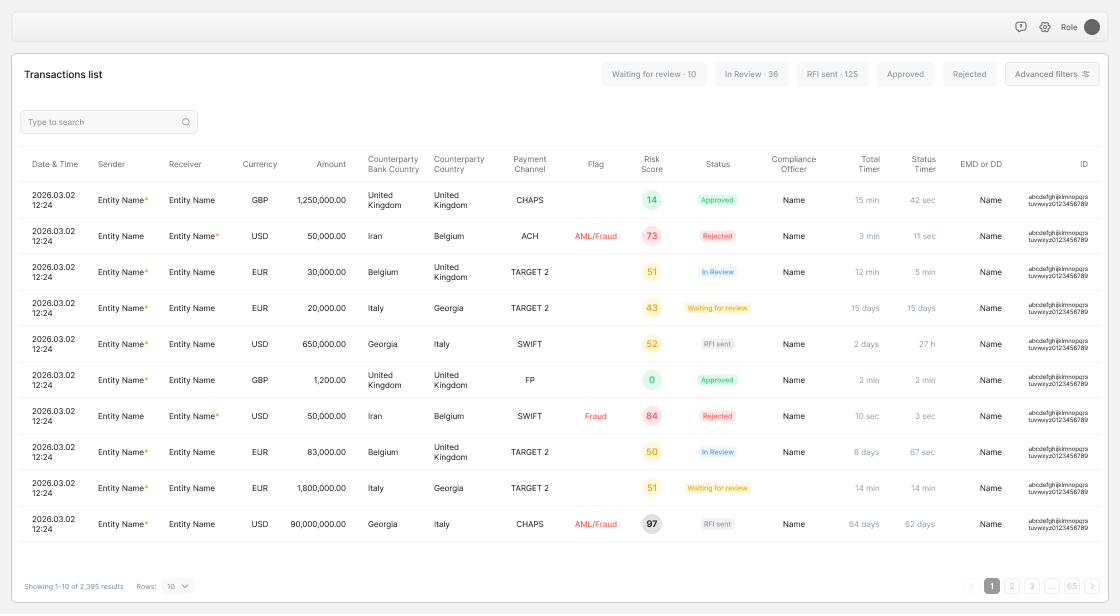
Conventional compliance is a relay race between systems. Onboarding lives in one tool, screening in another, monitoring in a third, investigations in a case manager, reporting in a separate template. Each handoff loses context.
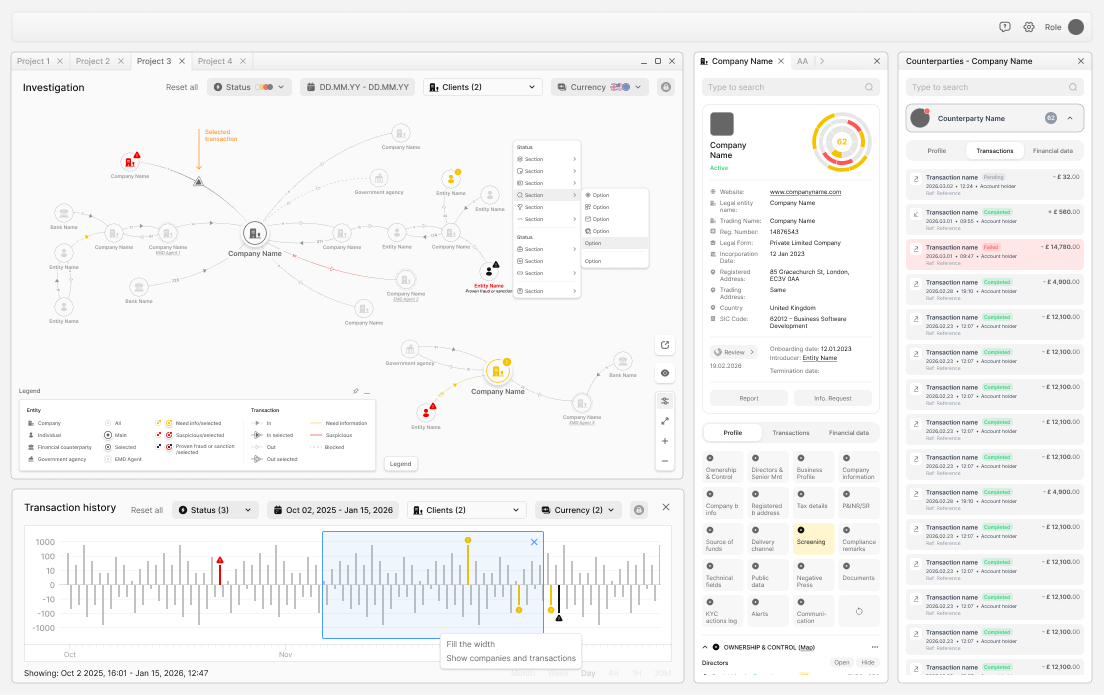
Springwood collapses the relay into a production line. The customer profile assembled at intake is the same record monitored against, the same record opened in investigation, and the same record drawn from to generate the SAR. There is no second copy.
- i.Live case objectIdentity, ownership, profile and behaviour as one record.
- ii.Connected panelsRisk, alerts, geography, devices & balances on one sheet.
- iii.Provenance trailEvery panel value links back to its source object.
- iv.Maker / checkerDecisions captured with approval routes attached.
- v.Audit-as-fileThe working record is the regulatory record.
Identity · ownership
Modules M.01 — M.02
Identity, drawn from source.
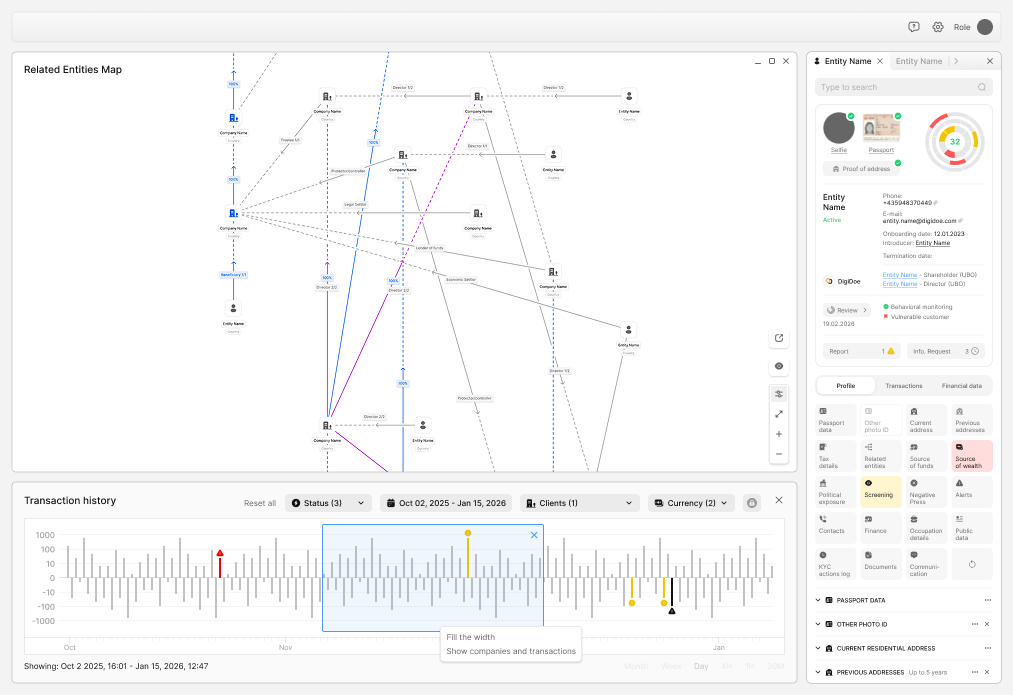
Document set complete
Who they are.
Who controls them.
Customer due diligence and beneficial-ownership resolution sit on the same record. Documents extracted once, validated once, scored once — then carried through every subsequent monitoring decision and investigation.
The relationship graph is interrogable: percentage ownership is calculated, nominee arrangements are flagged, control by other means is recorded. Changes to a beneficial owner re-trigger screening downstream automatically.
- i.Biometric capturePassport, ID card, NFC chip, liveness-tested selfie.
- ii.Document setProof of address, source of funds, source of wealth.
- iii.Ownership graphDirect, indirect, voting, control-by-other-means.
- iv.Change monitoringDirector, shareholder, controller updates rescreened.
- v.Behavioural baselineExpected activity captured at the start.
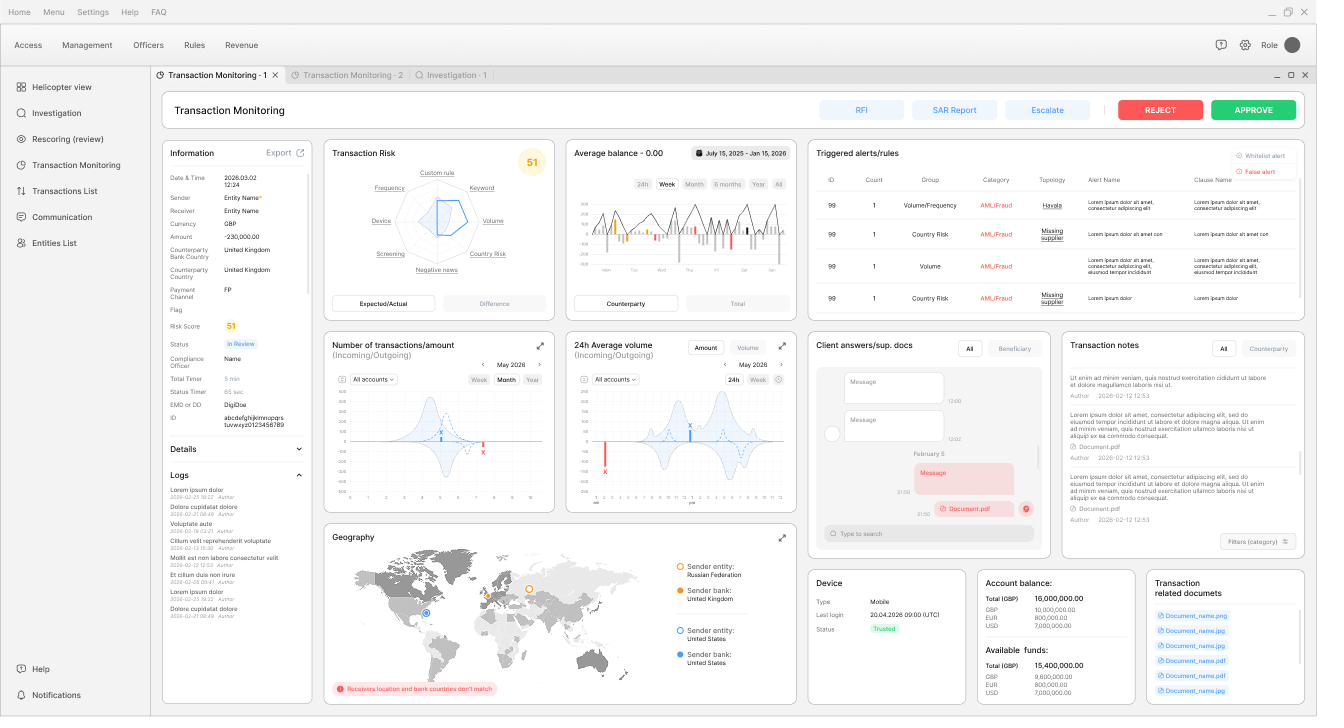
Monitoring · KYT
Module M.04
Activity in context,
not just thresholds.
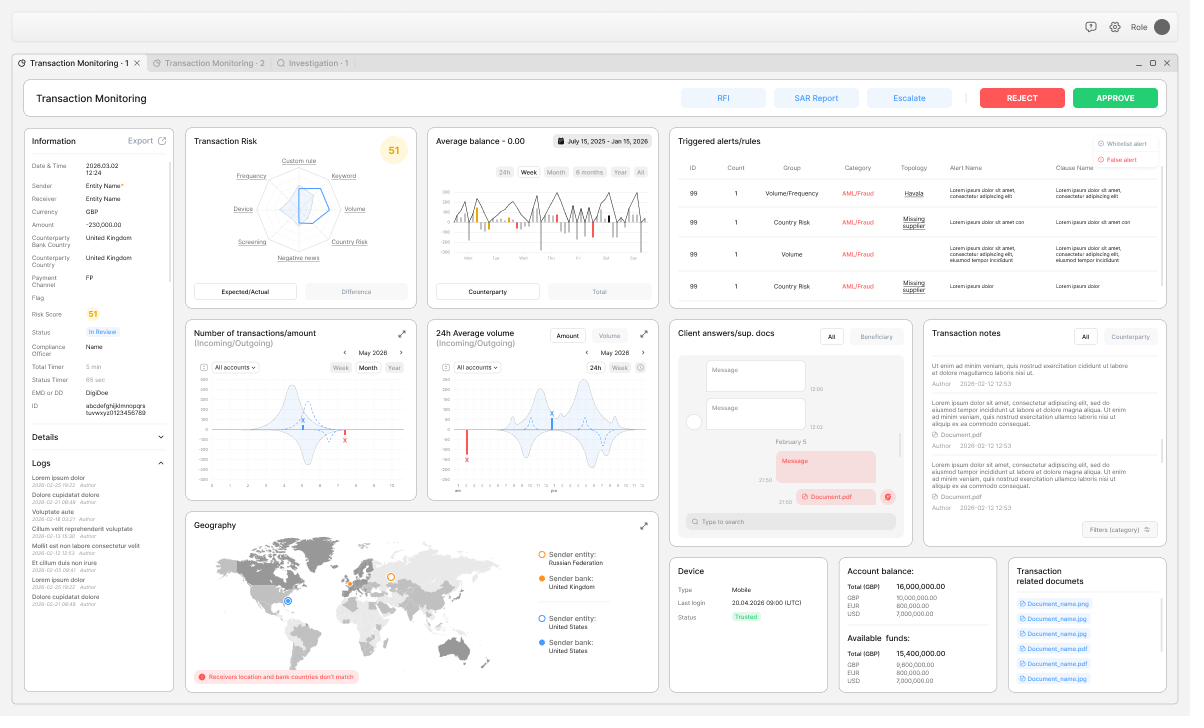
Decisioning sheet
The radar reads
six dimensions.
A transaction is assessed against the customer's declared profile, corridor and counterparty risk, channel typology, device and behaviour, screening exposure and negative-news state — not a single flat threshold. The radar is a quick read of where this transaction sits against expected, and the alert grid below it tells the analyst which rule fired and why.
Crucially, the case sheet is where the decision is made. There is no separate "investigation system" to copy into.
- i.FrequencyVelocity against declared activity profile.
- ii.VolumeAmount against expected baseline and corridor norms.
- iii.Country riskSender / bank / counterparty country exposure.
- iv.DeviceTrust signal, last login, behavioural anomaly.
- v.ScreeningSanctions, PEP, adverse risk on the parties.
- vi.Custom ruleInstitution-specific scenarios and typologies.
Status-timed
Casework · OSINT
Module M.05
Cases open with
the evidence attached.
Approval-routed
Judgement.
Not reassembly.
Conventional investigation is mostly file reconstruction. The analyst pulls statements, requests documents, runs OSINT searches, copies data into a working file, then begins the actual analysis hours later. Most of the time is spent before the thinking starts.
Springwood inverts the order. The network, the documents, the counterparties, the timeline and the prior alerts are already on the case when the analyst opens it. The job becomes the judgement: does this pattern, with this evidence, in this context, support a suspicion report?
- i.Entity networkCompanies, individuals, banks, agencies — connected.
- ii.Counterparty registerEvery party with transactions, status and reference.
- iii.Profile depthOwnership, control, addresses, regulator, history.
- iv.TimelineTransaction history charted with selected events.
- v.OSINT linksSource-bound external evidence attached to the file.
- vi.Approval routeMaker / checker / MLRO routes built in.
Six modules
One control layer
Six modules.
One control layer.
| Ref. | Module | Scope | Sheet |
|---|---|---|---|
| M.01 | Verify | Remote identity, document and liveness capture; address and database validation. | Fig. 02.A → |
| M.02 | Profile | Ownership, control, expected behaviour, source of funds and source of wealth. | Fig. 02.A → |
| M.03 | Screen | Sanctions, PEP, adverse risk, internal watchlists, counterparty exposure, rescreening. | Not shown |
| M.04 | Watch | Real-time and batch monitoring of payments, accounts, wallets, FX, settlements. | Fig. 03.A — 03.B → |
| M.05 | Investigate | Unified casework — AML, fraud, sanctions, onboarding, KYB and transaction review. | Fig. 04.A → |
| M.06 | Report | SAR / STR drafts, MLRO workflows, FIU bundles, restricted access, post-report monitoring. | Not shown |
| M.00 | Control | Policy rules, model governance, QA sampling, audit packs, retention, legal holds. | Substrate |
Sector register
Built for
Where volume and
risk are both rising.
| Ref. | Sector | Primary scope | Operating flow |
|---|---|---|---|
| i | Banks | CDD, KYB, sanctions, transaction monitoring, fraud review, investigations, SAR/STR, audit. | Onboarding → monitoring |
| ii | EMIs & payment institutions | Wallets, virtual IBANs, merchants, counterparties, payment flows, fraud typology. | Real-time controls |
| iii | Crypto & digital asset | KYC, KYB, wallet intelligence, on/off-ramp behaviour, sanctions exposure, ownership. | Wallet ↔ identity |
| iv | Law firms | Client due diligence, sanctions, complex ownership, asset tracing, enhanced investigations. | Engagement-led |
| v | Regulators & law enforcement | Supervised firms, suspicious reports, customer networks, transaction patterns, OSINT. | Investigation-led |
| vi | Funds & administrators | Investors, SPVs, trusts, source-of-wealth, redemptions, ownership, cross-border structures. | Lifecycle-led |
A smaller queue.
A stronger record.
Springwood is designed for institutions that need measurable compliance productivity without lowering standards. Discuss your workflow with the team.