Doc · 03 / Capabilities
— Capabilities · full coverageSheet 03 / 11
Verify. Monitor. Investigate. Report.
The Springwood capability set covers the full financial-crime lifecycle. The language is deliberately operational: each capability exists to reduce manual work, improve intelligence quality and produce a defensible working file.
- Coverage
- 10 capabilities
6 product modules - Domains
- KYC · KYB · KYT
OSINT · Fraud · SAR - Output
- Source-bound
working file
§ 01 / Identity · ownership
01.Section one
Verify · Profile · Screen
Capabilities 01 — 05
Verify · Profile · Screen
Capabilities 01 — 05
Identity, drawn from source.
Fig. 01.AEntity profile · related entities map
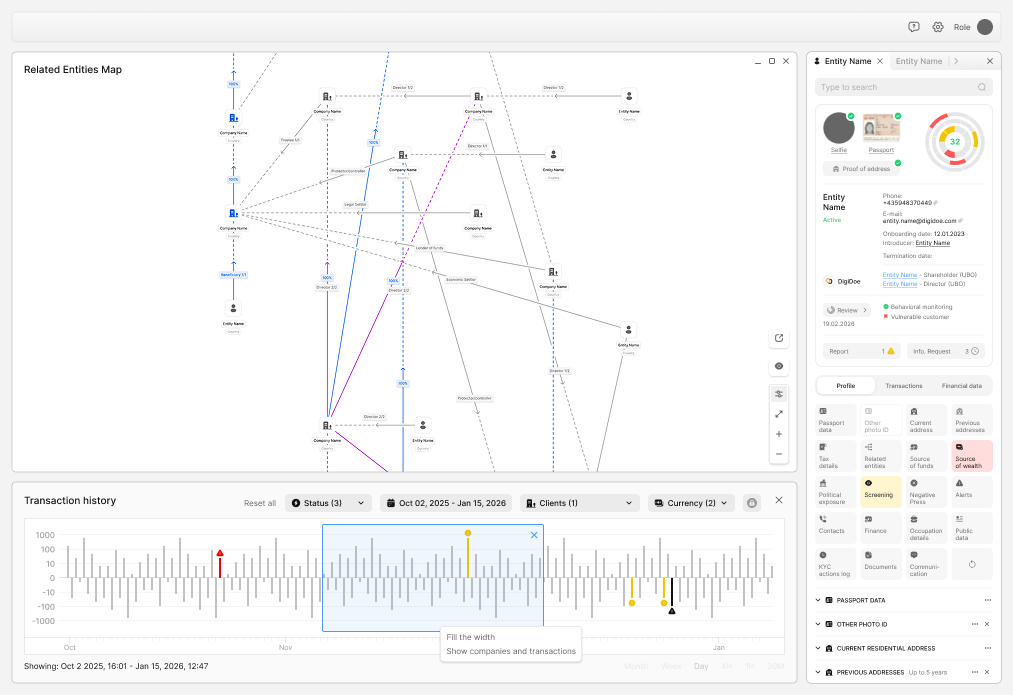
Caption ▸Identity capture, ownership resolution and ongoing screening sit on a single connected file. Related-entities map on the left, profile panel on the right — every fact carries provenance.
Verified inputsNFC · MRZ · Liveness
§ 01 / Capabilities
| Ref. | Capability | Scope | Module |
|---|---|---|---|
| C.01 | Remote identity & authorisation | Automated identity validation using biometric passport or ID, NFC chip data where available, MRZ extraction, selfie liveness, and comparison against government, commercial and internal sources. Document authenticity, address verification, authorisation workflow for sensitive actions. | M.01 Verify |
| C.02 | KYC & onboarding workflow | Risk-based journeys for individuals, directors, signatories, trustees, beneficiaries, politically exposed persons and high-risk customers. Expected activity captured at intake; source-of-funds and source-of-wealth files; low-confidence extraction routed to review; periodic and event-driven refresh. | M.02 Profile |
| C.03 | KYB & ownership intelligence | Business verification for companies, funds, trusts, SPVs, partnerships, foundations, public entities and complex cross-border groups. Direct and indirect ownership, voting rights and control-by-other-means logic, nominee handling, change monitoring. | M.02 Profile |
| C.04 | Sanctions, PEP & watchlist screening | Continuous screening across customers, beneficial owners, controllers, directors, signatories and counterparties. Batch and real-time; rescreening on list and profile changes; explainable matches; internal watchlists and restricted parties. | M.03 Screen |
| C.05 | AI OSINT & connection mapping | AI-assisted open-source and licensed-source analysis for adverse indicators, hidden relationships, corporate networks and media risk. Relationship mapping across persons, companies, addresses, accounts and devices. Source-linked summaries; human validation for material findings. | M.05 Invest. |
§ 02 / Monitoring · fraud
02.Section two
Watch
Capabilities 06 — 07
Watch
Capabilities 06 — 07
Activity in context.
Fig. 02.ATransaction monitoring · case sheet
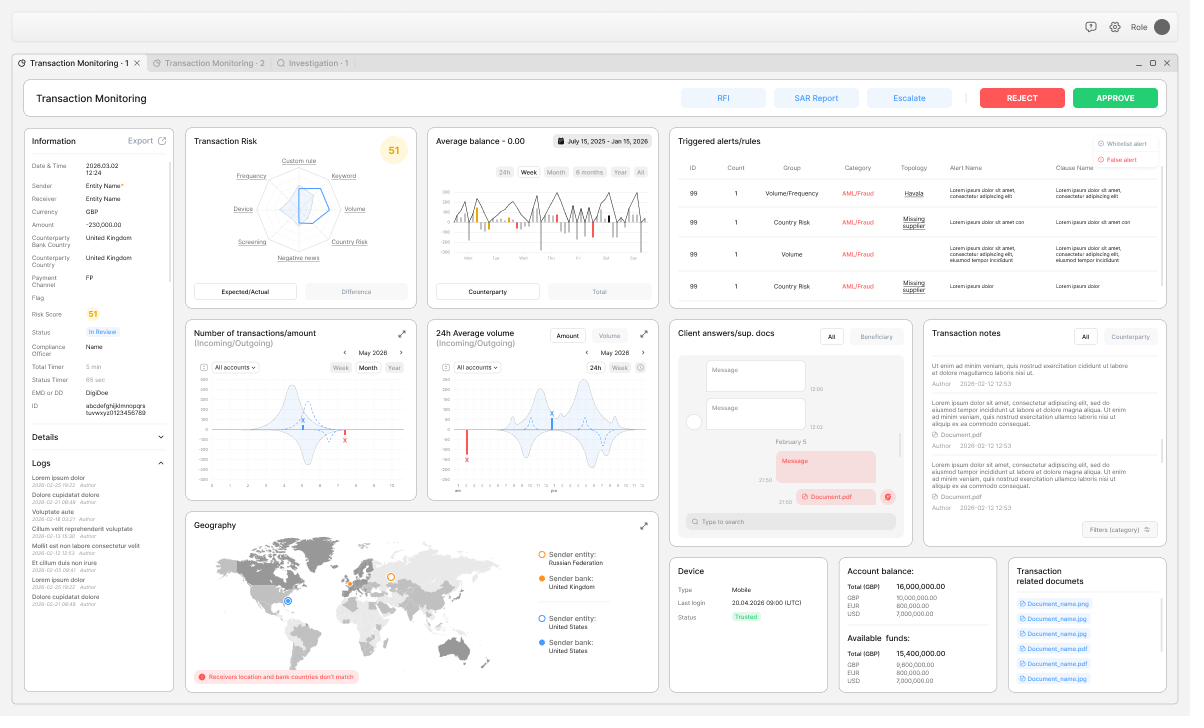
Caption ▸A single transaction opens with its full operating context: information panel, six-dimension risk radar, triggered alerts, transaction counts, geography, device trust, account & available funds, linked documents. Approve, reject, RFI, SAR Report or escalate — directly from the sheet.
Live contextDecisioning sheet
§ 02 / Capabilities
| Ref. | Capability | Scope | Module |
|---|---|---|---|
| C.06 | Transaction monitoring & KYT | Real-time and batch monitoring of payments, attempted payments, wallets, account movements, FX, settlements, capital movements and high-risk corridors. Expected-versus-actual analysis; counterparty, corridor, velocity and timing analytics; scenario, anomaly, graph and typology detection. | M.04 Watch |
| C.07 | Fraud prevention | Unified AML and fraud intelligence for APP fraud, mule networks, synthetic identity, account takeover, internal fraud, document fraud and unusual merchant or payment behaviour. Device, identity and behavioural anomalies; internal and external threat monitoring; fraud case escalation with supporting data. | M.04 Watch |
§ 02 / Sub-exhibit
Fig. 02.BQueue · transactions list
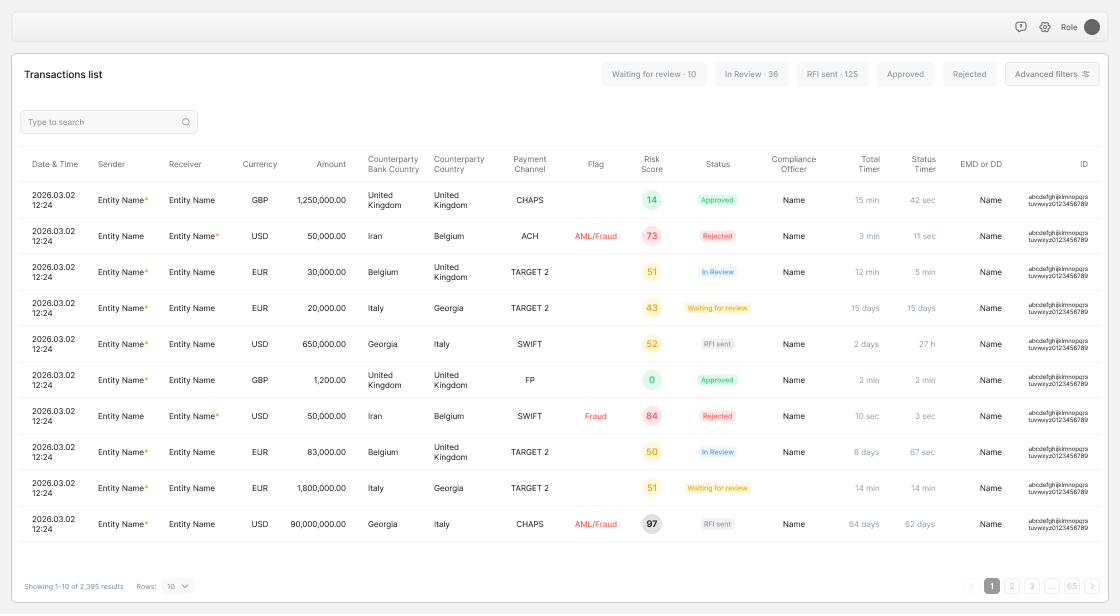
Caption ▸The queue view ranks the day's work by risk score and status timer. The analyst's first hour is spent on rows that need a decision, not on triage.
Operational queueRisk-ranked
§ 03 / Investigation · reporting
03.Section three
Investigate · Report · Control
Capabilities 08 — 10
Investigate · Report · Control
Capabilities 08 — 10
Cases open with the evidence
already attached.
Fig. 03.AInvestigation · entity-network workspace
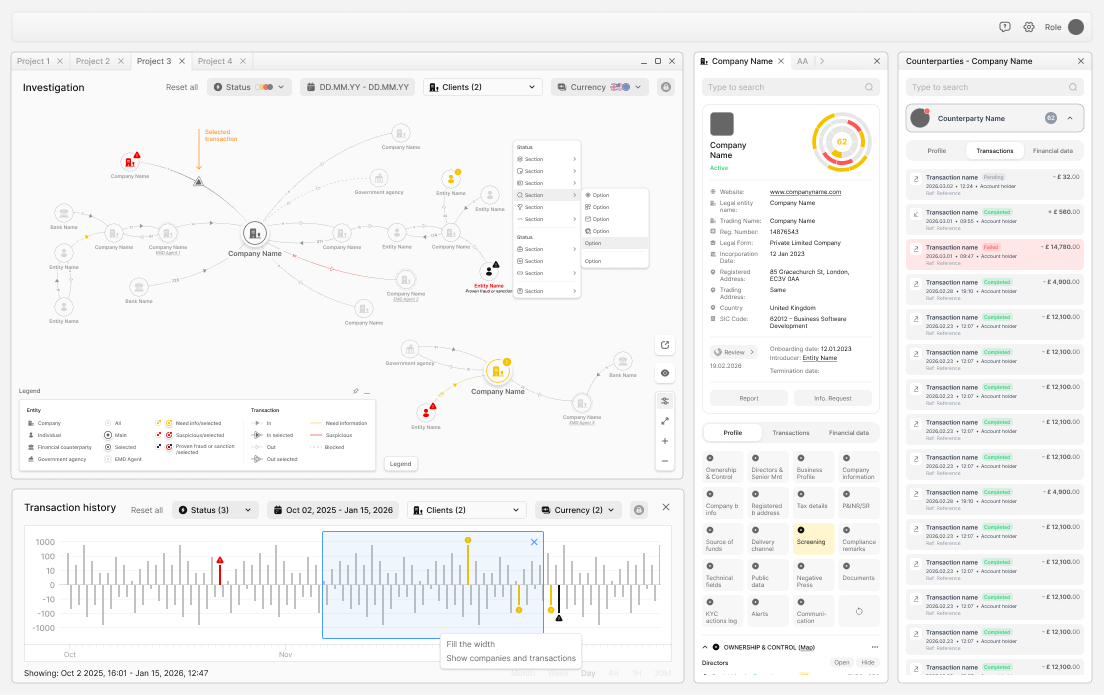
Caption ▸Investigation opens with the network already drawn, the counterparty register populated, the profile depth available and the timeline ready. The analyst arrives to judge, not to assemble.
CaseworkPre-assembled
§ 03 / Capabilities
| Ref. | Capability | Scope | Module |
|---|---|---|---|
| C.08 | Investigation workspace | An entity-centric workspace that brings customer files, ownership, transactions, alerts, OSINT, documents, notes, tasks and decisions into one case view. Unified queue across AML, fraud, sanctions and KYB; network visualisation; AI-assisted summaries and missing-evidence prompts; maker-checker, MLRO and senior approval routes. | M.05 Invest. |
| C.09 | SAR / STR & FIU reporting | Regulatory reporting workflow for suspicion assessments, report drafts, approvals, evidence bundles, FIU requests, redaction and post-filing monitoring. Jurisdictional templates; restricted-access case handling; no unsupported narrative statements; retention and audit pack generation. | M.06 Report |
| C.10 | Governance & audit assurance | Controls for policy rules, thresholds, model versions, scenario testing, validation, overrides, QA sampling, audit exports, retention and legal holds. Versioned rules; automated control testing; board and MLRO management information; reconstructable case and control records. | M.00 Control |
CTA / Capability briefing
Cover the same surface.
Fewer manual handoffs.
Springwood is designed to replace repeated analyst assembly work with controlled automation and exception-based review. Map your capability gaps with the team.